Free Speech
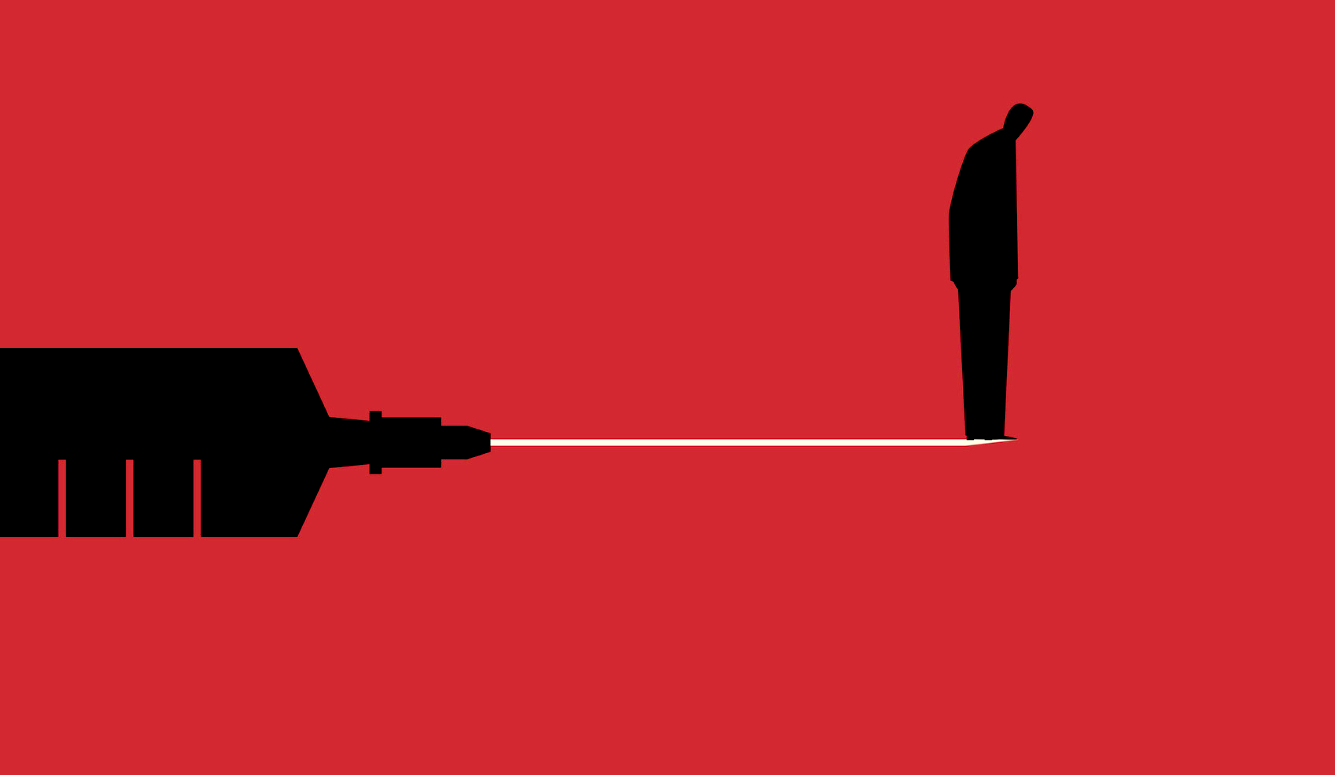
Denying Encryption to Terrorists Is a Fantasy
The Home Office could demand more surveillance abilities for law enforcement, but here it is difficult to see what they could ask for that they don’t already have.

The script for responding to Western terror attacks is now so predictable that they might as well publish a schedule in the TV listings. First we get the platitudes: “praying for” the affected city, liking Facebook statuses, and projecting flags onto buildings. Next there is the denial stage, where the commentariat implore us not to make assumptions about the attacker’s motives, because for all we know this was actually the work of Buddhist monks or the National Farmers’ Union. Then comes the hand-wringing over the potential racist backlash at the hands of the unstable, knuckle-dragging public, whose desire for an anti-Muslim pogrom can only be kept in check by loudly proclaiming that Islamic terrorists are not Real Muslims. Finally, once the emotion has died down, politicians can get on with doing what they do best — demanding more control over the internet.
After Khalid Masood murdered four people in London last month, Home Secretary Amber Rudd wasted no time in laying the blame at the feet of WhatsApp, insisting that secure messaging apps must not be a “place for terrorists to hide.” If this phrase seems oddly familiar, it is because former Prime Minister David Cameron was reciting a similar mantra shortly before 17 million Brexiteers derailed his career. As political slogans go, it is probably no worse than any other. It’s catchy, uses accessible and emotive language, and expresses a sentiment that few would outright disagree with. There is just one problem: what it demands is impossible. Not just politically unpopular or legally challenging—it quite literally cannot be done. The only technology that could stop people from communicating privately is a nuclear apocalypse.
Despite the breathless claims in the media, it is not yet known whether Masood actually sent a message just before the attack. The fact that his phone “connected” to WhatsApp means nothing. Instant messaging apps remain in contact with their servers almost continuously, even when no conversations are in progress, in order to be notified of incoming messages. But let’s assume that careful examination of the evidence does indeed suggest the existence of some final doomsday message. Let’s gloss over the likely reality that even if the message had been intercepted, it would have been too late to prevent an attack occurring only a few minutes later. Let’s also ignore the fact that Masood was not even a suspect, and would not have been under surveillance in the first place. Let’s give Mrs Rudd the benefit of the doubt, and accept at face value her belief that monitoring WhatsApp is the key to preventing future atrocities. How does she propose to achieve this?
We can probably rule out the nuclear option of banning encryption outright. Even politicians are hopefully not this stupid. For starters, encryption is just mathematics. A law against mathematics would be logically nonsensical—not to mention impossible to enforce — and most likely ignored by everyone, not just terrorists. Furthermore, encryption is absolutely everywhere: it is built into every browser and smartphone, used by operating systems as a defence against malware, mandated by the credit card processing industry, and enabled automatically on a vast range of websites from Google to Wikipedia. Modern processors even have dedicated hardware instructions to make encryption faster. A total ban on encryption would be like trying to roll back thirty years of technological development. They might as well just outlaw the internet altogether.
The Home Office could demand more surveillance abilities for law enforcement, but here it is difficult to see what they could ask for that they don’t already have. From the Regulation of Investigatory Powers Act 2000, to the “Snooper’s charter” in 2016, the British state already has some of the most draconian powers in the world. They can hack into phones or computers, force ISPs to record the online activity of their own users, and legally oblige anyone to disclose an encryption key that they are suspected of possessing. Whatever data exists, the government can get, and if it doesn’t exist, they can probably order someone to start collecting it. The only thing they can’t do is compel providers to decrypt data for which they don’t have the key, because the whole point of encryption is to make that impossible. All the legal powers in the world are not going to change that.

What we might see is some sort of partial ban, such as a law permitting encryption only if there is a “back door” for law enforcement. This will face two major problems. First, many apps are developed outside of the UK’s jurisdiction. ProtonMail is based in Switzerland; Signal is developed by a small company in California; Telegram was written by Russians, headquartered in Germany, and hosted on servers in undisclosed locations. WhatsApp is owned by Facebook, which does have a presence in the UK, but that could soon change — companies that really value privacy will close their British offices rather than weaken their software. The UK government cannot impose its laws on other nations, and even if those countries were willing to cooperate voluntarily, many of them have strong constitutional protections that would make it very difficult to force developers to redesign their own products.